Research published by mobile security specialist AdaptiveMobile claims all the extra complexity created by network slicing leads to new vulnerabilities.
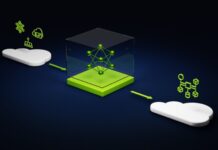
Network slicing involves the virtual partitioning of the RAN and core to create ‘slices’ of the network that can be tailored to specific use cases. It seems that virtual network functions spanning many slices have insufficient mapping between the application and transport layers identities. ‘This flaw in the industry standards has the impact of creating an opportunity for an attacker to access data and launch denial of service attacks across multiple slices if they have access to the 5G Service Based Architecture,’ says the press release.
“As more of the core network moves to the cloud and an IT-based architecture, so more suitable hacking tools become available for hackers,” said Dr. Silke Holtmanns, Head of 5G Security Research at AdaptiveMobile Security. “Currently, the impact on real-world applications of this network slicing attack is only limited by the number of slices live in 5G networks globally.
“The risks, if this fundamental flaw in the design of 5G standards had gone undiscovered, are significant. Having brought this to the industry’s attention through the appropriate forums and processes, we are glad to be working with the mobile network operators and standards communities to highlight these vulnerabilities and promote best practice going forward.”
You can access the full white paper here, which is reassuringly full of arcane jargon and baffling diagrams. The complexity of 5G NR networks, with all their virtualization, slicing and general mucking about, was always bound to create new vulnerabilities. Hopefully reports such as this will help to ensure the telecoms industry doesn’t sacrifice security in its desperation for 5G ROI.